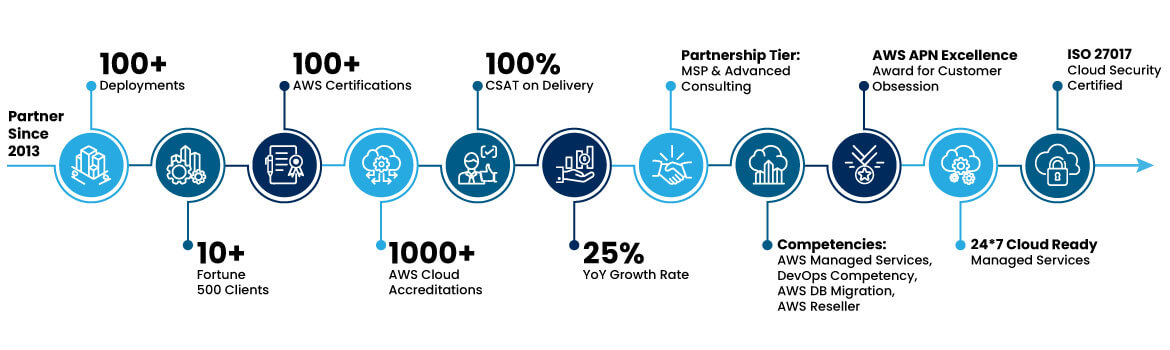
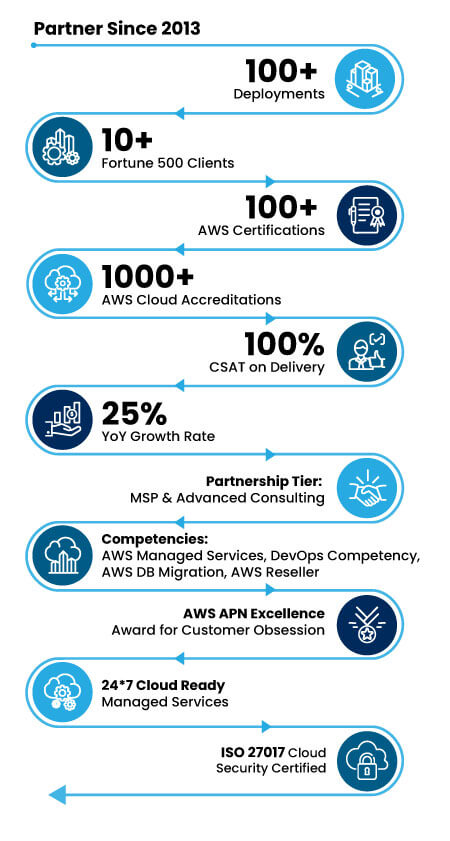
Our AWS Expertise and Experience
Moving to cloud computing can seem daunting, but, with the right approach, the benefits will far outweigh the issues you might face. You can overcome challenges that arise with the help of a trusted cloud consulting services provider such as Trianz, which is an Advanced Consulting Partner and Managed Service Provider for AWS. Also, our consultants are AWS-accredited in business and technology competencies.
With 1000+ AWS Cloud accreditations and 100+ AWS Certifications, we have expertise in some of the most complex and value-creating AWS programs in the world. In addition, our work with AWS has included leading-edge programs – for example, we were among a handful of partners to build on the new Athena Federated Query (AFQ) Extensions from AWS. Moreover, through our partnership, we combine technology and scalability to turn innovative ideas into business value – rapidly.
Trianz’ AWS Cloud Competency Journey
Copyright © 2024 Trianz
Benefits of AWS Cloud
By working with Trianz to get the most out of AWS Cloud, your business can achieve scalability, faster time to market and application development, improvements in productivity and security, cost reduction, flexibility, agility, better availability, and operational efficiency. Moreover, it will enable acceleration of your enterprise’s digital transformation.
Our Services
We cover the full spectrum of AWS Cloud consulting services, from assessments, strategy, and roadmap, to design, build, and migration – and from adoption, optimization, and management to data and analytics and security.
Cloud Strategy
Moving to AWS Cloud, or upgrading existing cloud services, takes a lot of planning to get it right. We work with you to assess your status and identify any gaps in capabilities or potential roadblocks; develop your unique cloud strategy; and deliver a comprehensive roadmap.
In addition, we incorporate the approach of combining AWS Platform as a Service (PaaS) and AWS Infrastructure as a Service (IaaS) into the strategy and plan. This translates into deploying digital experience and analytics applications on flexible cloud platforms, implementing agile and DevOps methodologies, and leveraging scalable, single sign-on, and risk-avoidant solutions to protect IP and customer data.

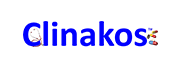
AWS Well-Architected Review
AWS Well-Architected Reviews ensure your cloud architecture aligns with best practices for optimal performance, security, and cost-efficiency. Trianz begins by assembling the correct stakeholders, gathering designs, addressing issues, and defining workloads. This foundational approach drives meticulous architectural reviews, with Trianz customizing recommendations using AWS Lenses. Our service outcomes are impactful—clients receive a detailed workload review report that includes comparisons, improvement summaries, risk categorization, and optional strategic approaches. Trianz further defines procedures for periodic reviews to ensure sustained alignment with AWS Well-Architected best practices. AWS Well-Architected principles align with Trianz's commitment to excellence throughout our processes and are invaluable to the outcomes we deliver.
 AWS Well-Architected Framework
AWS Well-Architected Framework
Cloud Migration
Our experienced consultants can help facilitate seamless migration of your on-premises data center so you can realize enhanced business agility, improved performance of your applications, and increased transparency in maintenance costs. We also leverage AWS capabilities to offer you app migration to serverless environments.
In addition, our end-to-end infrastructure migration services can help you with business-IT alignment, tools selection, and expertise to accelerate migration of legacy infrastructure to AWS and improve workforce productivity significantly. We also specialize in orchestrating and executing roadmap through different phases of the migration process to ensure success.
Trianz runs Microsoft workloads on AWS EC2 for multiple clients leveraging AWS services specifically designed to support Windows Server & SQL Server.
By combining Microsoft workloads on AWS EC2 Trianz provides reliability, scalability, security, and flexibility of AWS infrastructure with comprehensive support for Microsoft applications, offering businesses a powerful platform to deploy and manage their Microsoft-based solutions.
Cloud Security
When you move to the cloud, protecting your data – as well as your customers’ – should be a top priority. We offer a range of cloud security strategy services, including layered security, remote employee protection, and hybrid cloud security. With our strategic approach, you will get enhanced flexibility of enterprise data, automation for continuous compliance, and continuous security training.
Also, as far as the data is concerned, compliance with the GDPR, CCPA, PCI-DSS; in particular, Payment Card Industry Data Security Standard (PCI-DSS) is critical for the storage of sensitive payment card information. Our PCI-DSS compliant consulting service on AWS offers you legacy compliance in cloud data migrations, self-assessment questionnaire (SAQ) assistance and audit, and improved data security.
Cloud Optimization, Operations Management, and Managed Services
Trianz can work with you to manage and optimize your AWS Cloud infrastructure to drive efficiency, increase ROI, reduce costs, and improve scalability. Our consultants can assist you with managing cloud consumption, capacity, performance, and cost through continuous monitoring; dynamic, scalable operations; control and visibility of OpEx spend, compliance, outcomes, and SLA-driven governance; and built-in security compliance. By leveraging our IT service management (ITSM) and IT operations management (ITOM) solutions, your business can instead focus on customer growth and satisfaction.
In addition, a robust DevOps strategy will maximize an organization’s productivity by streamlining the organizational structure (processes, practices, and systems) needed to eliminate waste within the product development workflow. As part of DevOps, we offer a range of container scaling services on AWS, including container orchestration, as well as chaos engineering to reduce your overheads and expedite the software development lifecycle (SDLC).
We also provide Cloud Operations Consulting Services to help organizations establish standard operating procedures for long-term cloud operations. This entails identifying and defining the processes and procedures to optimize IT services within the cloud environment.
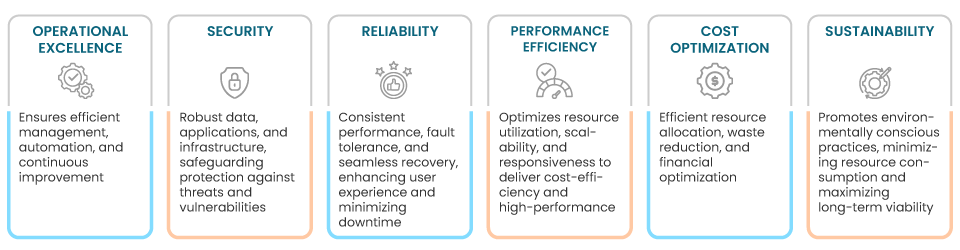
Cloud Data and Analytics
Analytics is the key to driving value through data. Our research shows that digital champions – what we call the 7% of organizations that are successful with their digital transformations – weave advanced analytics into their operational processes and work culture. This shapes their strategy, business requirements, business model design, data structure, measurement, and reporting to digitally transform their operations.
Analytics becomes even more of a game changer when you add automation, machine learning (ML), and artificial intelligence (AI) to take existing data and technologies and optimize them in real-time. AWS is an ideal platform for automated data analytics, with low-cost data storage solutions and task-specific compute nodes that negate the need for ITOM workloads. We design efficient, analytics solutions through the Trianz Analytics on Cloud implementation service for AWS Cloud. Through Analytics on Cloud Ecosystem, we harness the power of ML and AI for a range of services, such as total cost of ownership (TOC) forecasting and automated business intelligence (BI).
AWS Data and Analytics Services Included in Trianz Analytics on Cloud Ecosystem for AWS
Copyright © 2023 Trianz
Our AWS Innovation
We fuse technology and scalability to move beyond ideas to practical innovations. By working with Trianz, you can access our innovative tools:

AWS AFQ Connectors
In partnership with Amazon, our AFQ Extensions enable quick analysis of data from heterogeneous sources to offer faster time to market, a low-cost POC, and a quick scale to production – all with fewer lines of code.

Concierto.cloud
Through our integrated cloud and infrastructure operations management platform, we fuse independent software vendor applications to orchestrate seamless cloud infrastructure operations and provide a comprehensive view of infrastructure and applications.

Arxway
Our bastion host server application is designed to ensure the security of your Amazon Elastic Compute Cloud (Amazon EC2) instances, allowing you to access the Amazon Virtual Private Cloud (VPC) from anywhere, anytime from your organization’s VPNs.

EVOVE
We designed this accelerator to speed up migration, increase efficiencies, and tap into our expertise gained through hundreds of cloud migrations, resulting in 60% less time spent on migration and at least 50% reduction of costs.